Windows Password Recovery - artificial Intelligence attack
Artificial Intelligence Attack is a brand-new type of attack developed in our company. It is based upon a social engineering method and has never been implemented in password recovery applications yet.
This one is mostly used when the hashes are imported from the local computer. Artificial Intelligence attack scans the local computer, indexes and creates the list of found words and passwords, analyzes them, upon the results of the analysis produces user's preferences, performs the mutation of the found words and, based on all that, attempts to recover the passwords.
This attack allows, without resort to time-consuming and costly computations, to almost instantly recover certain passwords encrypted with hash functions. The basic idea behind the Artificial Intelligence attack is that an average user very often chooses similar words and word combinations or follows the same password generation rule when creating one's passwords. With that in mind, we could attempt to figure that rule out and guess the original password.
Although this sounds somewhat abstractive, in the reality the attack clearly splits into four successive steps.
- Initiating the collection of private data. Here comes into action the password retrieval and indexation module, which looks for all available and hidden in the system passwords entered by the user at any moment of time. Those include network access passwords, ICQ, email, FTP, Windows account passwords, server passwords, LSA Secrets, etc.
- Launches the data collection and indexation module. During the execution of this step, we analyze the activity of the user (or all users, if the indexation module selected is different than Light) in the system. Next, based upon that, we generate the list of words - potential passwords selected from the text files, archives, Internet browsers' history, email correspondence, etc.
- Includes the semantic analysis module for the database of found passwords and the list of potential passwords.
- On the final stage, the data analysis module will perform the mutation of the words and attempt to pick the passwords.
At the beginning of the attack, the program will search the system for all passwords it knows of. For that purpose, there are currently 32 mini-modules for decrypting system, mail, browser, messenger, archive and other passwords. Then there goes the file and data indexation, along with the course of which the program generates a potential attack dictionary. The third module breaks the passwords and words into pieces, out of which in the last module it will assemble new combinations for picking and guessing the original password.
On average, with the least indexation and mutation levels, the attack time may vary between 1 minute and 10-15 minutes, depending on the network activity of the user. On a home computer, the entire route normally takes not more than 2-3 minutes. Naturally, the more complex is the mutation and indexation level, the more efficient will be the search. However, reaching the topmost indexation and analysis level may take hours and even days, depending on the speed of the password validation algorithm and the number of users in the system.
If your Artificial Intelligence attack runs very slow, you may need to remove your program's cached passwords. For example, if the total amount of the cached passwords exceeds 10000.
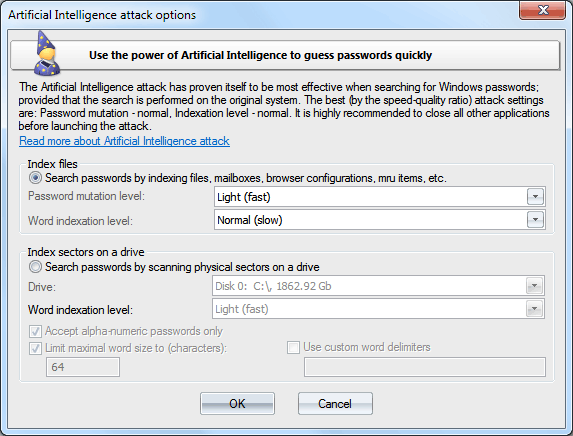
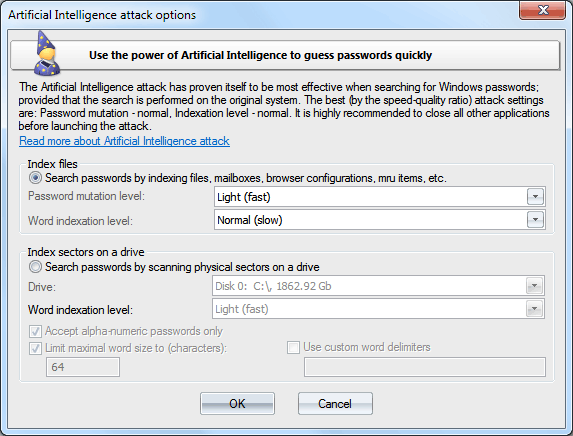
The Artificial Intelligence attack has proven itself to be most effective when the search is performed on the original system. Only two options are available here: password mutation depth and word indexing level. The most preferred options for running a speedy attack are Light:Light. For a deeper (and at the same time slower) search, set these options to Normal or even Deep. The duration of an Artificial Intelligence attack also depends on the configuration of your system, your network load, and other factors.
It is highly recommended to shut down all other programs before launching the attack!
Windows Password Recovery version 9.5 now comes with a brand new feature which allows searching for passwords by indexing raw sectors on the selected drive. This feature works for both LM and NTLM hashes, looking for ASCII and UNICODE passwords alike. You can change some advanced search options here. For example, the 'Word Indexation level' option sets an additional mutation on all found passwords. Be careful though, walking through all sectors of the target drive with this option set to 'Hard' may take quite a time. Note that the sector-based scanning algorithm is not effective against drives which have a full-disk encryption set on. Like BitLocker or TrueCrypt, for example.