Windows Password Recovery - online recovery
Online recovery (developed by Passcape Software) finds passwords using Internet search engine servers. It deals fairly well with short and frequently-used passwords. Among its drawbacks are low operating speed and poor suitability for handling large hash lists.
Online recovery has been developed by Passcape Software and is an improved online password finder. To find passwords, the program consecutively submits a special search request for each hash to a search engine and then downloads the password files found and analyzes their contents. Online recovery is relatively slow; therefore, it is appropriate for small hash lists. In addition, the passwords found are usually limited to simple vocabulary and short combinations. One way or the other, this attack can be quite useful; for example, when auditing passwords, as a simple vulnerability detector for certain systems.
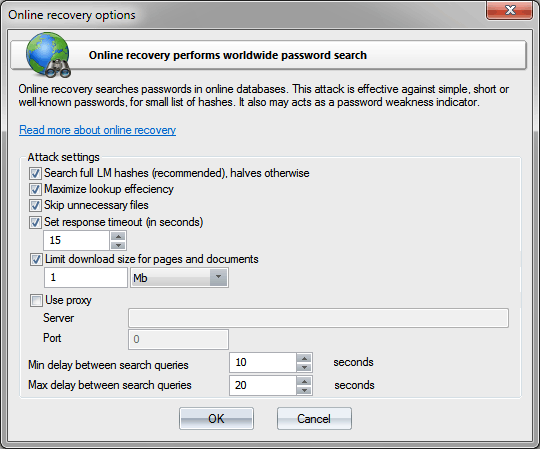
Online recovery options
- Search full LM hashes - use the entire 16-byte hash when searching LM hashes. If this option is not set, the search will be carried out over the 8-byte halves. To ensure more efficient search and get rid of some stray traffic, it is recommended that this option is set. It is ignored when searching NT hashes.
- Maximize lookup efficiency - increase password lookup efficiency not affecting the attack speed. It is also recommended to always set this option.
- Skip unnecessary files - do not check some unnecessary files if they are suspected to not contain passwords.
- Response timeout - set the maximum allowed Web resource response time.
- Limit download size - limit download file size. Some hash databases have enormous size, even despite that often they do not contain passwords. Therefore, for slow Internet connections and to restrict stray traffic, it is recommended to set a limit on the size of download pages. Unfortunately, there is no way to figure out what is in the data to be downloaded; therefore, this option is determined exclusively by your preferences and capabilities.
- Use proxy - use a proxy server for looking up passwords
- Min/max delay between search queries - minimum and maximum delays between two consecutive requests to the search server. Some search servers may reject search requests if they go in series from the same IP address with a very short time interval (normally less than 10 seconds). Despite that Windows Password Recovery has an internal request randomizer, which allows dropping this delay significantly (to as little as 1 and 2 seconds respectively), the safe values when a search request will be definitely processed by the server are min=15 and max=30 seconds. Certainly, the attack speed depends is in direct relation to these two options.
Be careful! Online recovery may generate a lot of Internet traffic!