Wireless Password Recovery - combined dictionary attack
Combined dictionary attack (developed in our company) is great at recovering passwords that consist of 2,3 and even 4 words. This type of recovery is very similar to the simple dictionary attack, except that instead of using a single word here we use a combination of words or a phrase created by combining words from specified wordlists. To successfully utilize this attack, set at least two wordlists and the rules for generating passwords. You can set the regular wordlists used in the simple dictionary attack, but it is recommended to use rather small ones with the most common words.
Combined attack sets a certain limit to the number of wordlists that can be used; that's not more than 4. Thus, the general limitation of this attack is that only password phrases of not more than 4 words can be recovered using this tool.
Another essential drawback is the wide range of phrases generated. And, as the consequence, the proportional increase of the time spent on the password validation. Keep in mind that when generating passwords that consist of 3 or 4 words, the generation process takes considerable time. This is especially important when testing 'slow' hashes, that is WPA-PSK.
The software comes with a special wordlist for the combined attack.
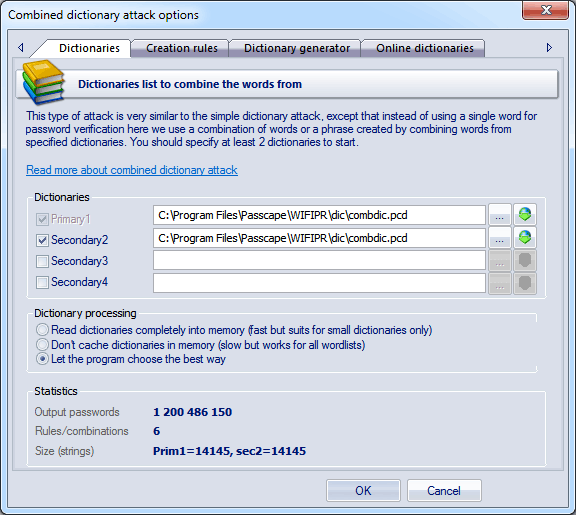
Dictionaries
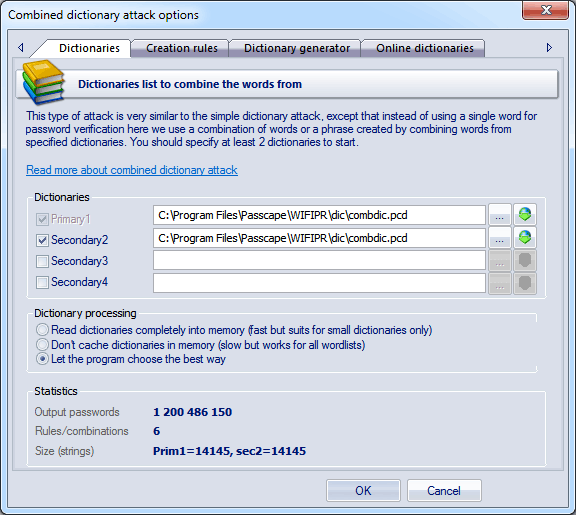
The way the combined attack works is really simple. For example, if you have set two wordlists, the program will generate the passwords as follows: it will take the first word from the first wordlist and glue it with the first word from the second wordlist, then with the second word, and so on until the end. Then it checks the second word from the first wordlist and goes the same route, and so on.
The order of the words in the phrases to be created depends directly on the order of the source dictionaries. In our second example, if we swap the primary and the secondary dictionaries, at the output we will obtain a completely different set of phrases.
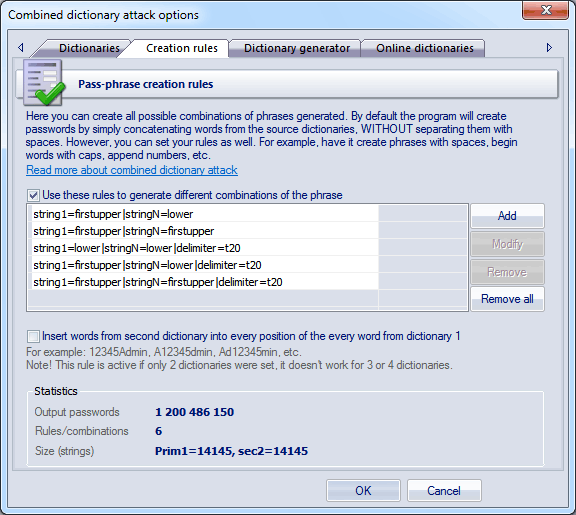
Mutation rules
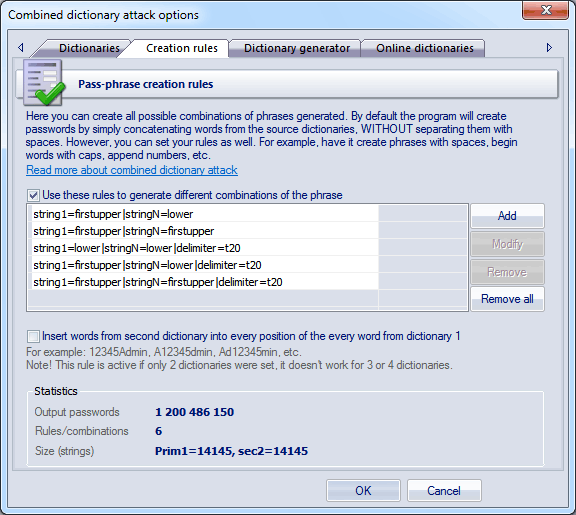
Passwords created by the combined dictionary attack are generated according to special rules that are to be set on the second tab. By default, when password generation rules are disabled, the program generates passwords by simply gluing up the words from the source dictionaries, without separating them with space. For example, of the two words are 'my' and 'computer', you will get 'mycomputer'.
If word insertion option is set, the program additionally creates passwords by inserting words from the second dictionary into every position of the word from dictionary 1. For example, if the first dictionary's word is Admin, and the word from the second dictionary is 12345, the program will generate the following passwords:
12345Admin
A12345dmin
Ad12345min
Adm12345in
Admi12345n
And so on for all words of the second dictionary. Then goes another word from dictionary 1, etc. The option is active if only 2 dictionaries were set.
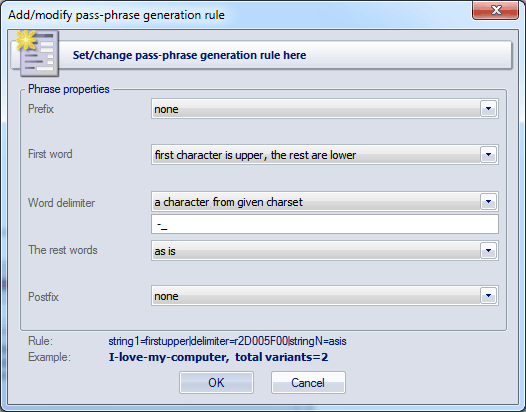
The generation rules are made to extend the password search options. For example, Mycomputer, MyComputer, MY COMPUTER, my-computer, etc. There are special rules available for this purpose; you don't have to know the syntax of them, for the mutation rule creation dialog is simple and intuitive.
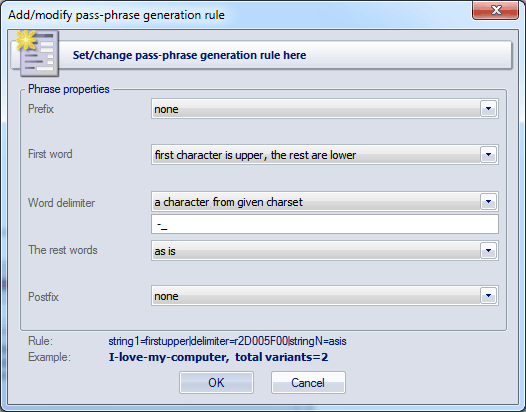
Each mutation rule consists of five elements:
- Prefix - text that will appear before each phrase. This element can be a character from given charset, plain text string, one digit between 0 and 9 or a number. For instance, if you set a one-digit prefix, the phrases created with this rules will look as follows: '0aaabbb', '1aaabbb' ... '9aaabbb'.
- First word - the action to be performed over the first word of each phrase. There are only four options. Namely: leave intact as is in the dictionary, convert all characters to lowercase, convert all characters to uppercase or capitalize only the first letter of the word.
- Word separator. It may be absent. Then all the words will be concatenated. Example: 'aaabbb', 'aaaccc','aaaddd', etc. You can otherwise set a custom separator; e.g. the '-' character: 'aaa-bbb', 'aaa-ccc','aaa-ddd'. Or you can set a range of characters.
- Other words. With this attribute, similarly to 2., you can set rules for the other words of a phrase.
- Postfix - text that will finalize each phrase. For example, if you set Postfix to the '?' or ' ?', all phrases created with this rule will have the question mark at the end.
The more password generation rules you set, the more chances you have to guess the password. But, on the other hand, the more time you will have spent on the attack.
The 'Statistics' group shows the average size of a dictionary, number of words in source dictionaries, the total number of passwords being generated and other helpful information
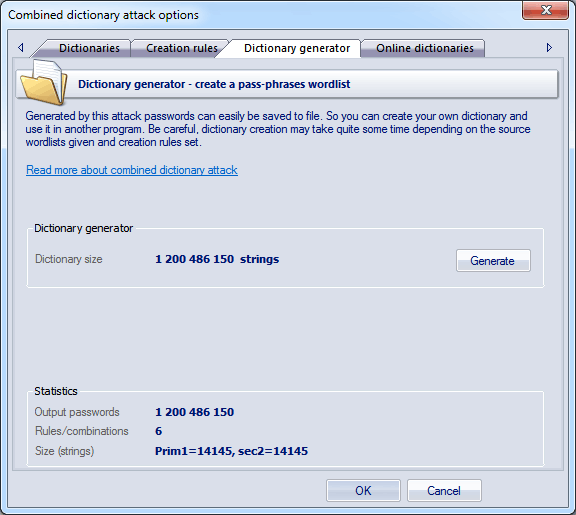
Dictionary generator
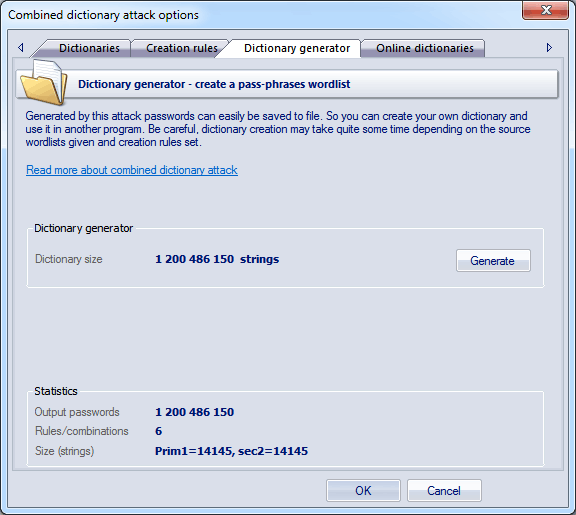
The third tab of options serves for creating combined attack-based wordlists.