Wireless Password Recovery - mask attack
Mask attack is an irreplaceable tool when you know a part of the password or have any specific details about it. For example, when you know that the password consists of 12 characters and ends with the qwerty, it is obvious that brute-force the entire 12-character range of passwords is useless. All that would be required in this case is to guess the first 6 characters of the sought password. That is what the mask attack is for.
In our case, we could define the following mask: %c%c%c%c%c%cqwerty. That means that the program would check the following combinations: aaaaaaqwerty, aaaaabqwerty, aaaaacqwerty .. zzzzzzqwerty. If the original password is 'secretqwerty', it perfectly hits our range.
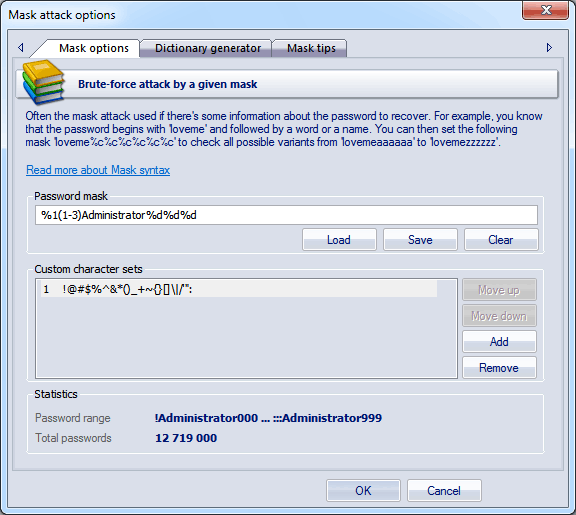
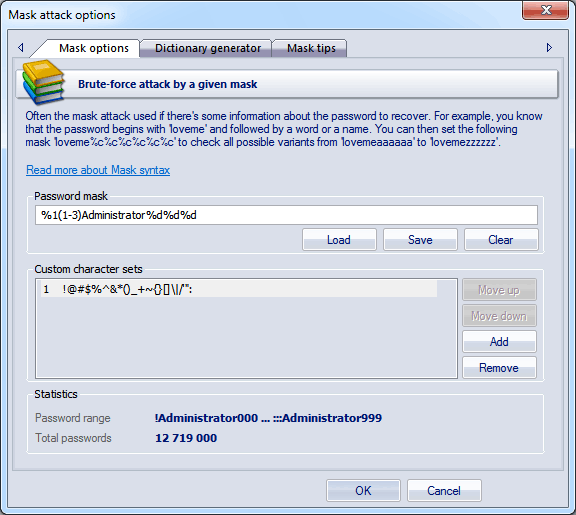
The password mask field is used for setting the rule, by which the program will try to recover the password. If the mask is set correctly, below you should see the range of characters generated by the mask. User-defined masks can be saved to disk. You can also use the mask tool to generate a wordlist to be used in other applications.
The mask syntax is quite trivial and consists of static (unmodifiable) and dynamic (modifiable) characters or sets. Dynamic characters/sets always have a leading %. For example, if you set the mask secret%d(1-100), the program will generate 100 passwords (secret1, secret2: secret100).
Wireless Password Recovery supports the following dynamic mask sets:
| %c |
lower-case Latin characters (a..z), 26 symbols |
| %C |
upper-case Latin characters (A..Z), 26 symbols |
| %# |
full set of special characters (!..~ space), 33 symbols overall |
| %@ |
small set of special characters (!@#$%^&*()-_+= space), 15 symbols |
| %? |
all printable characters with ASCII codes of 32..127 |
| %d |
one digit (0..9) |
| %d(x-y) |
numbers between x and y inclusive |
| %r(x-y) |
user-defined characters with serial ASCII codes between x and y |
| %r(x1-y1,x2-y2...xn-yn) |
set of several non-overlapping sequences of ASCII characters. Useful for defining custom character sets; e.g., of OEM characters. |
| %[1..9] |
a character from user-defined charset 1..9 |
| %[1..9](min-max |
user-defined range of variable length (from min to max). You can set up to 9 your own custom character sets. |
| %w(wordlist) |
a word from a given wordlist (a full path is also allowed) |
Examples:
| test%d |
will generate password range test0..test9, 10 passwords total |
| test%d(1980-2007) |
test1980 .. test2007, 28 passwords |
| test%r(48-57,97-122) |
test0 .. testz, 36 passwords |
| %#test%# |
_test_ .. ~test~, 1089 passwords |
| admin%1(1-5) |
admina .. adminzzzzz, where %1 is user-defined charset 1 (a..z) |
| %1%1%1pin%2%2%2 |
aaapin000 .. zzzpin999, %1 is user character set a..z and %2 is second user-defined charset which contains characters 0..9 |
| %w(c:\dic\names.dic)%d |
check words from names.dic with a digit at the end |
By switching to
Dictionary generator tab, you can generate your own dictionary by a given mask, and save it to disk.
The third tab of the mask options contains a short description of the mask syntax and a couple of simple examples.